This article describes updates being made to the ISO 14971 Standard in the new draft version released for comment in July 2018.
There are two versions of ISO 14971 that are currently available. The first is the international version: ISO 14971:2007. The second is the European normative version: EN ISO 14971:2012. There is also a new draft being created by the TC210 committee for release in 2019.
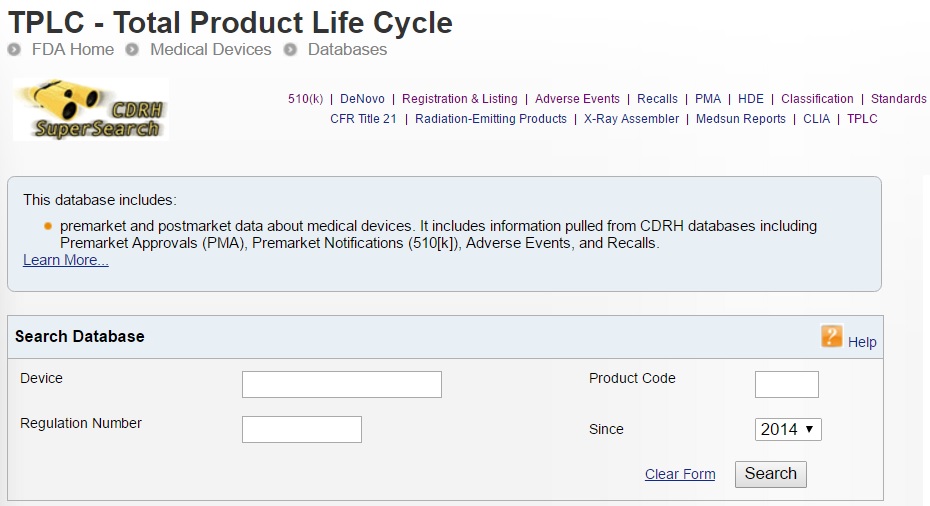
Explanation of the different versions of the ISO 14971 standard
In 2000, the first edition of ISO 14971 was released as the international standard for risk management of medical devices. In 2007, the second edition of ISO 14971 was released. When new international standards are released, a European normative version is also released. The “European Norm” or EN version is intended to identify any gaps between the international standard and the requirements of the applicable European directives (i.e., the MDD, AIMD, and the IVDD). These gaps historically were included in the ZA annex at the end of the EN version. However, in 2009 this annex was split into three annexes (i.e., ZA, ZB, and ZC) to address each of the three directives separately. In reality, the 2009 annex only differed concerning the directive referenced. In 2012, a new EN version was released. This new standard included seven deviations, which were controversial. These deviations were intended to identify contradictions between the directives and the international standard, but the interpretations were not agreed with by companies or most of the Notified Bodies. Ultimately, the seven deviations were required to be addressed in the risk management files for any medical device that was CE Marked.
What changed between ISO 14971:2007 and ISO/DIS 14971:2018?
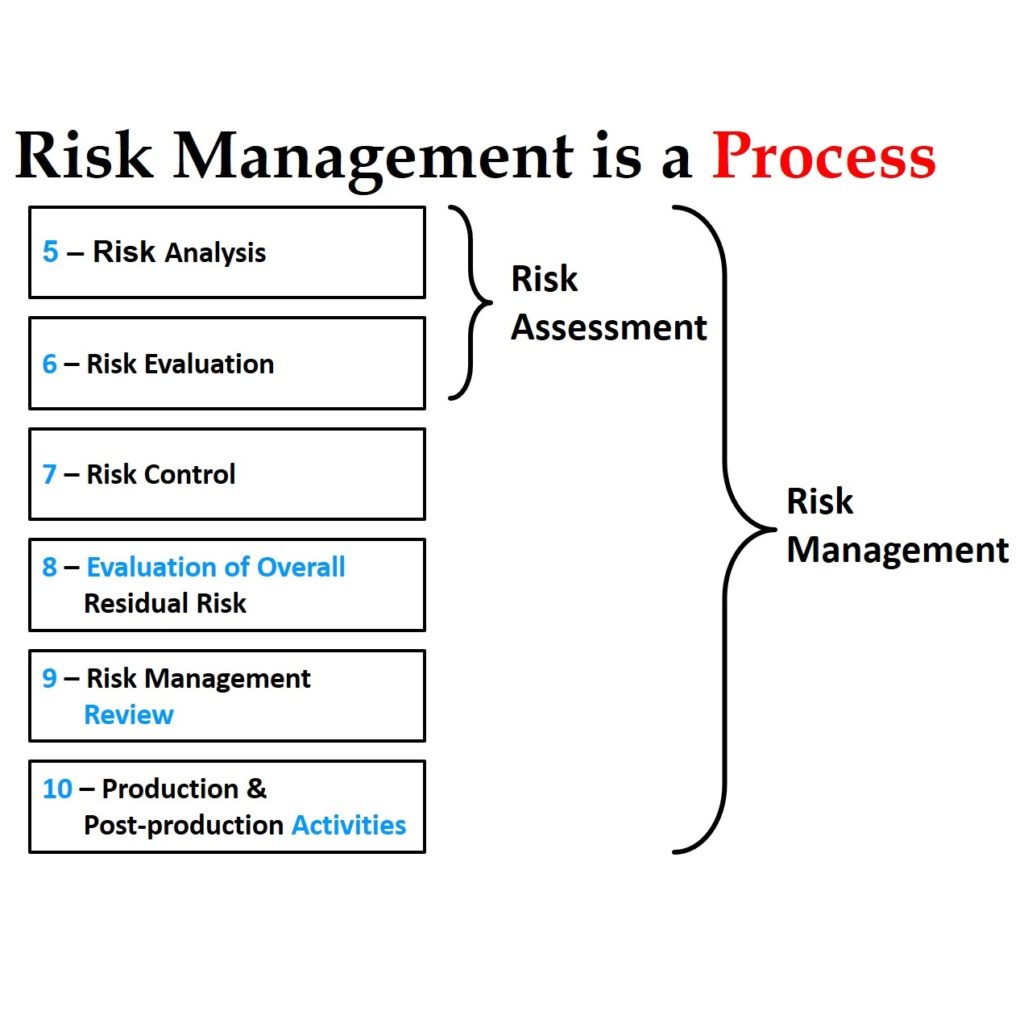
The TC210 working group assigned to update the ISO 14971 standard (JWG1) was tasked with improving guidance for the implementation of ISO 14971. Still, the committee was also tasked with making these improvements without changing the risk management process. Also, the committee was asked to move the informative annexes at the end of ISO 14971 from the standard to the guidance document ISO/TR 24971. Therefore, in July, the committee released a draft for comment and voting. Draft versions are identified with the prefix “ISO/DIS.” The ISO/DIS 14971 standard released in July has only three annexes: A) Rationale for the requirements, B) Risk management process for medical devices, and C) Fundamental risk concepts (formerly Annex E). The other seven annexes were moved to the draft of ISO/TR 24971. The reason stated for moving these Annexes to the guidance document was to make future revisions to the guidance easier to implement because it is a guidance rather than a standard. However, there were also some objectionable recommendations in the informative annexes that were the subject of deviation #3—ALARP from Annex D.8 vs. “As far as possible,” in the first indent of section 2 of Annex I in the MDD.
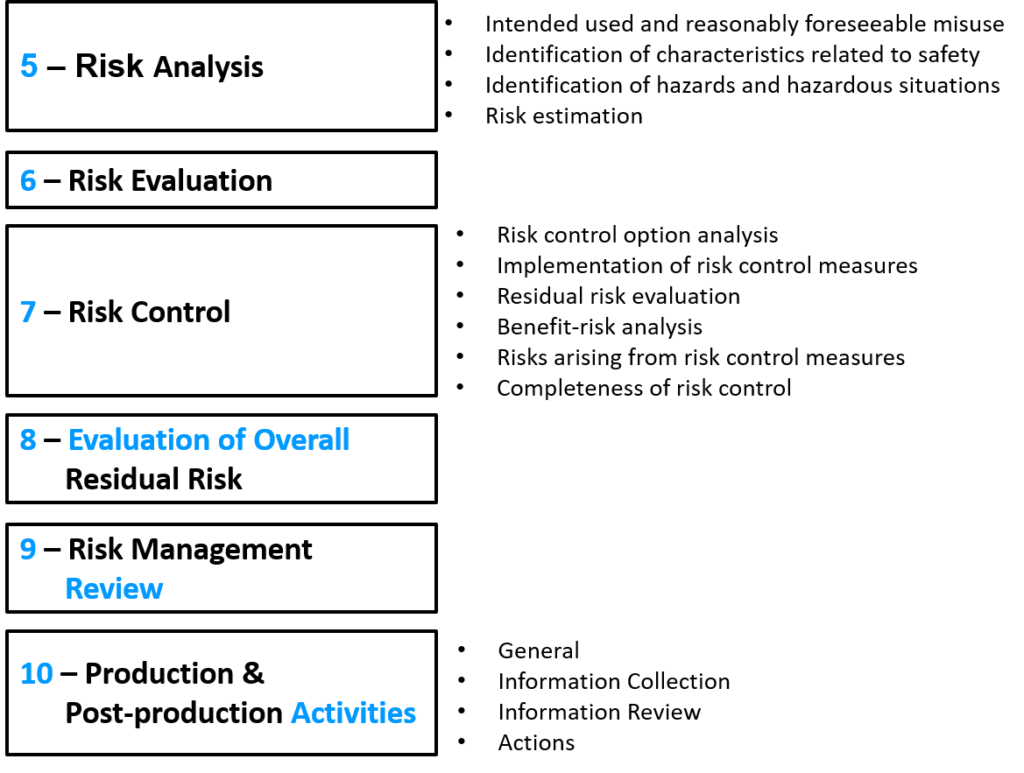
Although the committee was tasked to make improvements in the implementation of ISO 14971 without changing the process, the new draft has subtle changes in the process. Most of these changes can be identified quickly by reviewing the updated risk management flow chart provided in Figure 1. The updated flow chart now has two places where risks are evaluated. The first place is identical to the original Figure 1, but now the associated section is clarified to be specific to evaluating individual risks. The second place in the flow chart is new and specific to the evaluation of overall residual risks. The draft standard also states that different acceptability criteria and methods of evaluation may be used for each evaluation phase in the process. There have also been subtle changes to the names of process phases:
- Section 7.4 is now “Benefit/Risk” analysis instead of “Risk/Benefit” analysis—although the draft flow chart does not reflect this.
- Section 9 is now “Risk Management Review” instead of “Risk Management Report”
- Section 10 is now “Production and post-production activities” instead of “Production and post-production information”
There is also more detail in the diagram under the phases for 1) risk analysis, 2) risk control, and 3) production and post-production activities.
Three new definitions are introduced in the draft standard: 3.2, benefit; 3.15, reasonably foreseeable misuse; and 3.28, state of the art. The section for identification of hazards, Clause 5.4, was reworded and expanded to consider the reasonably foreseeable sequences or combinations of events that can result in a hazardous situation. The draft standard now states that your risk management plan must also include a method to evaluate the overall residual risk and the criteria for the acceptability of the overall residual risk. In the section for risk estimation, Clause 5.5, the draft standard states that if the probability of the occurrence of harm cannot be estimated, the possible consequences shall be listed for use in the risk evaluation and risk control. The risk control option analysis priorities in section 7.1 are updated to match the new MDR, Regulation (EU) 2017/745, nearly exactly. In section 9, risk management reports were changed to risk management review, and the Clause now requires determining when to conduct subsequent reviews and when to update reports. This emphasizes the requirement to continuously update risk management documentation with input from production and post-production information. This mirrors the emphasis on continually updating post-market clinical follow-up in Regulation (EU) 2017/745, Annex XIV, Part B, Section 5, and continuously updating clinical evaluations in Regulation (EU) 2017/745, Annex XIV, Part A, Section 1.
Will ISO 14971:2019 address the 7 Deviations in EN ISO 14971:2012?
The new MDR, Regulation (EU) 2017/745, revised and clarified the wording of the essential requirements in the MDD. The MDR attempts to explain the requirements for risk management files of CE Marked products, but the MDR remains different from the requirements of ISO 14971. Unfortunately, because the ISO/DIS 14971 was not intended to change the risk management process of ISO 14971:2007, there will continue to be “deviations” between the MDR and standard.
Some people have tried to use ISO/TR 24971, the risk management guidance, as the official interpretation of how the risk management standard. However, the guidance is also a product of the TC210 committee, and it does not meet all requirements of the MDD or the MDR.
The new draft does, however, include changes that address some of the deviations in EN ISO 14971:2012. Below, each of the seven variations is listed, and hyperlinks are provided to other articles on each deviation.
- Negligible Risks – The word “negligible” was only in one location in the body of the standard as a note referring to Annex D.8. In the draft, Annex D was removed and relocated to ISO/TR 24971, and the note was eliminated from Clause 3.4—now Clause 4.4 in the draft. The draft should fully resolve this deviation.
- Risk Acceptability – Clause 7 was renumbered to Clause 8 in the draft. Still, the title of this Clause was also changed from “Evaluation of overall residual risk acceptability” to “Evaluation of overall residual risk.” However, if you read the Clause it still refers to determining the acceptability of risks. In note 2 of Annex ZA of the draft, it states that determining acceptable risk must comply with Essential Requirements 1, 2, 5, 6, 7, 8, 9, 11, and 12 of the Directive. The draft should fully resolve this deviation.
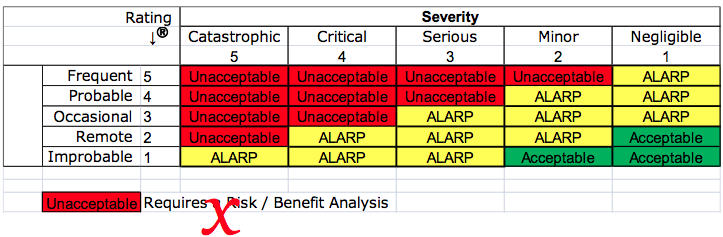
- ALARP vs. “As far as possible” – The European Commission believes that the concept of “ALARP” implies economic considerations, and some companies have used economics as a reason for not implementing certain risk controls. ALARP was eliminated from the notes in the risk management plan clause and by moving Annex D.8 to ISO/TR 24971 and adding note 1 in Annex ZA. The draft should fully resolve this deviation.
- Benefit/Risk Analysis – The contradiction in requirements between the International Standard and the MDD, as it relates to determining when a benefit/risk analysis must be conducted, has not been updated. The draft does not resolve this deviation. Companies that CE Mark products will need to perform a benefit/risk analysis for all residual risks and all individual risks—despite the wording of the standard.
- Risk Control – The contradiction in requirements between the International Standard and the MDD, as it relates to determining when risk controls must be implemented. The International Standard gives companies the option to avoid the implementation of risk controls if the risk is acceptable. At the same time, the MDD requires that risk controls be implemented for all risks unless the risk controls create additional risks that increase risks, or the risk controls do not reduce risks further. The draft does not resolve this deviation. Companies that CE Mark products will need to implement risk controls for all individual risks—despite the wording of the standard.
- Risk Control Options – The intent of Clause 6.2 in ISO 14971:2007 was likely to be the same as the MDD. However, the European Commission identified the missing word “construction” as being significant. Therefore, to prevent any misunderstandings, the TC210 committee copied the wording of Regulation (EU) 2017/745. The draft should fully resolve this deviation.
- IFU Validation – Again, to prevent any misunderstandings, the TC210 committee copied the wording of Regulation (EU) 2017/745. However, the examples of information for safety (i.e., warnings, precautions, and contraindications) were not included. Hopefully, the final version of the 3rd edition will consist of these examples. Clause 8, evaluation of overall residual risk, was also reworded to state, “the manufacturer shall decide which residual risks to disclose and what information is necessary to include in the accompanying documentation to disclose those residual risks.” The draft should fully resolve this deviation.
Recommendations for your Risk Management Process?
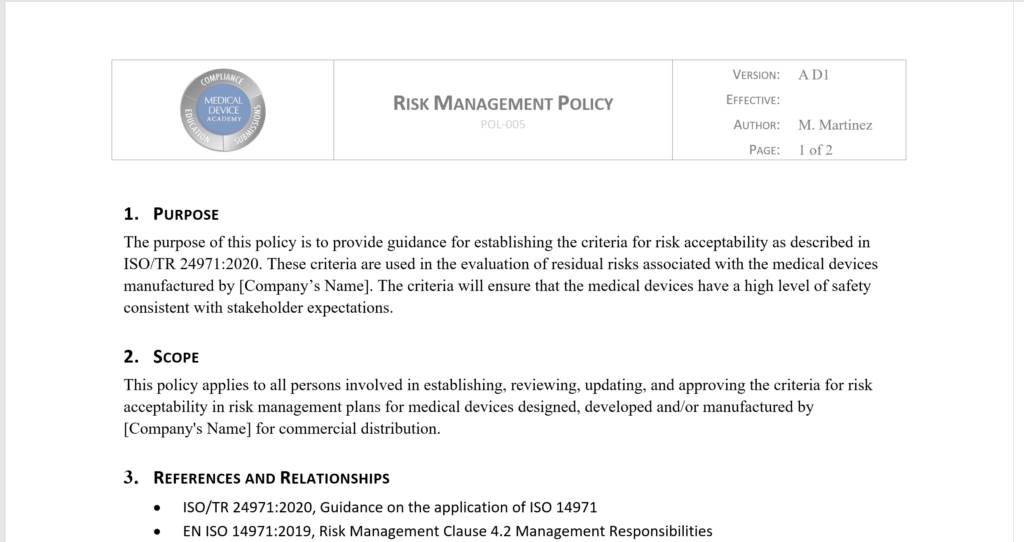
The most important consideration when establishing a risk management process for medical devices is whether you plan to CE Mark products. If you intend to CE Mark products, then you should write a procedure that is compliant with the current requirements of the MDD and future requirements of Regulation (EU) 2017/745. Therefore, the seven deviations should be addressed. Also, you need to maintain compliance with the current version of the standard.
I recommend creating a process based upon the newly updated process diagram in the latest draft. The process should begin with a risk management plan. For your plan, you may want to create a template and maintain it as a controlled document. It could also be part of your design and development plan template, but the plan should include each of the following risk management activities:
- Hazard identification
- Risk estimation
- Risk evaluation
- Risk control option analysis
- Risk control verification of effectiveness
- Benefit/Risk analysis
- Evaluation of overall residual risk
- Risk management review
- Production and post-production activities
Your procedure should also be integrated with other processes, such as 1) design control, 2) post-marketing surveillance, and 3) clinical evaluation. Your procedure must indicate the priority for the implementation of risk control options. The best strategy for ensuring risk control priorities are compliant is to copy the wording of the new EU Regulations verbatim. Your process should include performing benefit/risk analysis. You should also define your process for risk management review. Your review process should specify when subsequent reviews will be done, and when your risk management report will be updated. Finally, you should identify a post-market surveillance plan for each device or device family, and use that post-market surveillance data as feedback in the risk management process.
The one element that appears to be weakly addressed in the body of the standard is the requirement for traceability of each hazard to the other aspects of the risk management process. Although traceability is mentioned in Clause 3.5 of the 2nd edition, and Clause 4.5 of the draft 3rd edition of ISO 14971, that is the only place is mentioned in the body of the standard. Traceability is mentioned several more times in Annex A, but the focus seems to be on the risk management file. Companies need more guidance on how to achieve this traceability. The appropriate place for this guidance is probably in ISO/TR 24971. Still, in order to maintain this documentation, a software database will likely be critical to maintaining traceability as changes are made during design iterations and after commercialization. This type of software tool is also needed to expedite the review of risk management documentation during a complaint investigation.
Which Risk Analysis Tool should you use?
In Annex G of ISO 14971:2007 and the EN 2012 version, there are five different risk analysis tools described. The word “described” is emphasized because informative annexes are not “recommended.” The committee that created the 2nd edition of ISO 14971 wanted to provide several suggestions for possible risk analysis tools to consider. However, each tool has strengths and weaknesses. Additionally, the widespread use of the failure-mode-and-effects analysis (FMEA) tool in the automotive and aerospace industries has spread to the medical device industry, and companies seem to believe that regulators prefer the FMEA tool. This is not true. Companies should be trained in all of these tools, and training should consist of more than just reading Annex G, and the tools should be used where they are most beneficial. My recommendations are below:
- Preliminary Hazard Analysis (PHA) – This process is critical during the development of design inputs. It is also the most underutilized analysis tool. I have not seen a single example of this tool written in a procedure by any medical device company. I believe this process should be continuously updated as part of training new design team members and should be both product and project-specific.
- Fault-tree Analysis (FTA) – This process is a top-down approach to risk analysis. It is heavily utilized by transportation engineers when intersections are designed, and accidents are investigated. This tool depicts risk analysis pictorial as a tree of fault modes representing each possible root cause for failure. At each level of the tree, fault mode combinations are described with logical operators (i.e., AND, OR). The information displays the frequency of each fault mode quantitatively. Therefore, when you are investigating a complaint, the tree can be used to help identify possible fault modes that may have been the root cause of device failure. You may also be interested in the standard specific to Fault tree analysis (FTA): IEC 61025:2006.
- Failure Mode and Effects Analysis (FMEA) – This process is a bottom-up approach to risk analysis. The automotive and aerospace industries heavily utilize it. This tool systematically lists all failure modes in groups organized by component. Risks are estimated based upon the severity of effect, probability of occurrence, and detectability. Over time, the FMEA process split into three tools: 1) process FMEA (pFMEA), 2) design FMEA (dFMEA), and 3) use FMEA (uFMEA). The first is ideal for analyzing and reducing risks associated with the manufacturing of devices. In particular, the detectability factor can be linked closely with process validation. The second evolved from the realization that the detection of a risk after the device is in the user’s hands does not reduce risk. A risk reduction only occurs if detectability is proactive. Therefore, this was stated in Annex G.4, and companies began to eliminate detectability and continued to use FMEA as their primary tool. Due to the widespread familiarity with the FMEA tool, usability FMEAs became popular for documenting risks associated with the use of a device. Unfortunately, the only real advantages of a dFMEA and uFMEA are familiarity with the tool. You may also be interested in the standard specific to FMEA: IEC 60812:2018.
- Hazard and Operability Study (HAZOP) – In addition to the risks of using devices, there are also risks associated with the production of devices. Processes related to coating, cleaning, and sterilization are all processes that typically involve hazardous chemicals. The chemical and pharmaceutical industries use HAZAP as a tool to analyze these process risks and prevent injuries. You may also be interested in the standard specific to HAZOP: IEC 61882:2016.
- Hazard Analysis and Critical Control Point (HACCP) – This process is primarily used by the food industry to prevent the spread of contaminated food supplies. Even though medical device manufacturers do not typically use it, it should be considered as a tool for managing the supply chain for devices. This model is useful when manufacturing is outsourced, or secondary processing is conducted at second and third-party suppliers. Since many FDA inspectors started in the food industry as inspectors, this is also a method that is supported by the FDA as a risk control process for outsourced processes.
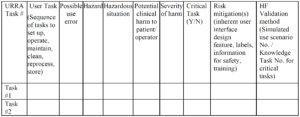
How to document your risks?
For simple devices, risk management documentation is a burdensome task. For complex devices, a spreadsheet could include hundreds of lines or more than even one thousand individual lines. Also, the requirement for traceability requires additional columns in a table. Therefore, it becomes nearly impossible for you to include all the required information on a page that is 11 inches wide. If you expand your page to 17 inches wide, the size of your font will need to be very small. If you make a change, your spreadsheet can be challenging to update quickly. You could purchase a 43” widescreen TV for your monitor, or you can use dual monitors for your display, but changes remain challenging to implement without a mistake.
You need to stop relying upon spreadsheets. Use a database, and don’t use Microsoft Access. Purchase a database that is designed to document design controls and risk management traceability. If your company has software expertise, develop your software tool to do this. You should also design standardized templates for exporting your reports. By doing this, it will only take minutes to create an updated report when you make design changes. If you describe the risk management activities as notes in your software, the description of these activities can also be automatically converted into summary pages for each report summarizing that risk management activity. You can even prompt the user to answer questions in the software to populate a templated document. For example, you can prompt users to input subsequent updates of your risk management reviews, and that can be automatically converted into a summary paragraph. This reporting capability is especially helpful when responding to FDA review questions asking for cybersecurity risks.
Additional Training Resources for ISO 14971
The risk management training webinar has been completely rewritten for the second time (i.e. the first time was on October 19, 2018). The newest version will be a two-part webinar series. Part one of two will focus on Clauses 1 through 7.1 of the ISO 14971:2019 standard. Part two of two will focus on Clauses 7.2 through 10. We selected Clause 7.2 to begin the second part of this webinar series, because it marks the beginning of the verification of the risk controls your company has implemented (i.e. – Post “Design Freeze”). Part 1 will be hosted live on March 29, 2022 @ 9-10:30 am EDT, and Part 2 will be hosted live on April 5, 2022 @ 9-10:30 am EDT. Both sessions will be recorded if you are unable to participate in the live sessions.
SYS-010, Medical Device Academy’s Risk Management Procedure, is compliant with EN ISO 14971:2019. The procedure includes templates for documentation of design risk management and process risk management. The procedure is also compliant with ISO/TR 24971:2020 and Regulation (EU) 2017/745. Both the two-part risk management training webinar, and the risk management procedure, are included in Medical Device Academy’s turnkey quality system.