Supplier Audit – Where should you spend your time?
In this article, you will learn how to spend your time during a supplier audit. We’ll teach you what is important and what you can skip.
Which suppliers need a supplier audit?
Before you start scheduling supplier audits, you should first decide which suppliers you need to audit. You are required to use a risk-based approach for supplier quality management but have specific recommendations. We recommend that you create five risk-based supplier quality categories:
- Critical suppliers
- Crucial suppliers
- Off-the-shelf component suppliers
- Service providers
- Consultants
Your critical suppliers are contract sterilizers, contract manufacturers, and contract packagers. Your crucial suppliers are suppliers manufacturing custom components or subassemblies. Off-the-shelf components speak for themselves, but examples of service providers include a company doing plating and other secondary processes. The last supplier category, but not the least, is the consultant category, such as the quality system auditors you hired to do an internal audit.
Which supplier categories require a supplier audit?
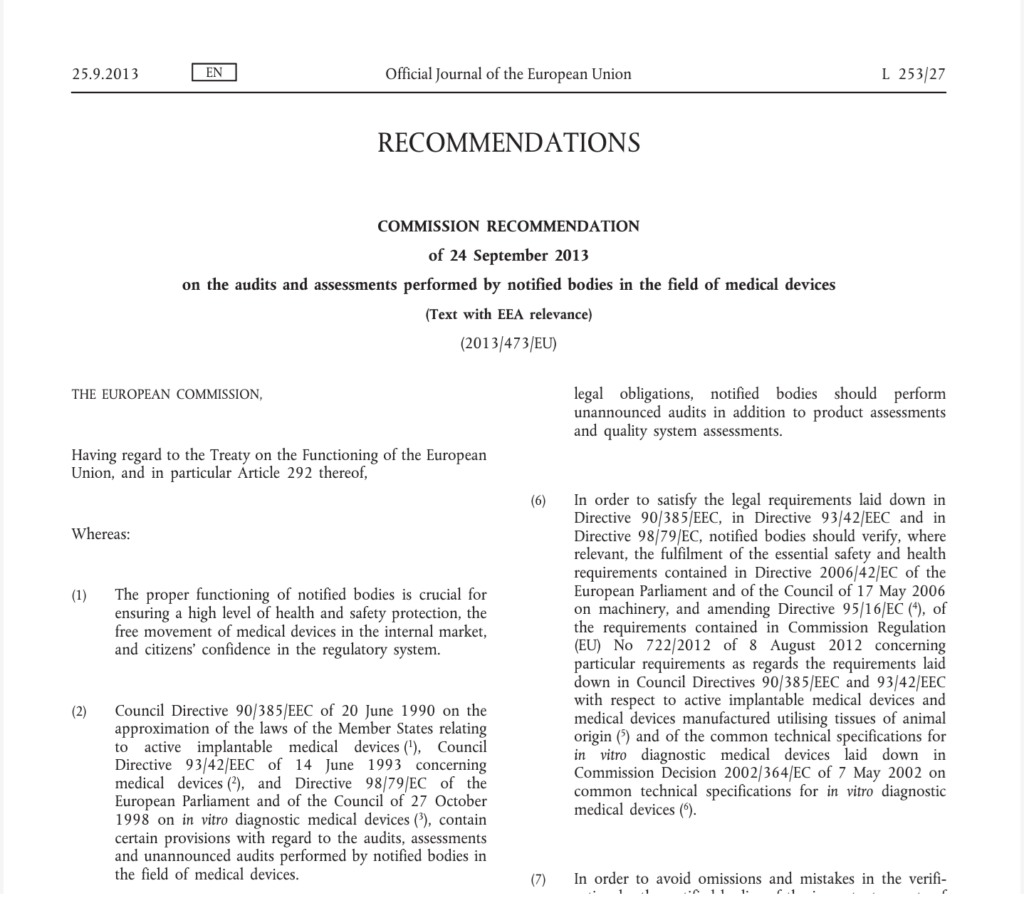
The FDA regulations don’t specifically require supplier audits. However, if an inspector finds any nonconformities among your purchased components, you will need to demonstrate how you have addressed the quality issues. If the corrective actions taken are not sufficient, you will need to conduct supplier audits as part of your corrective action plan or effectiveness check. Other countries have different expectations with regard to supplier auditing, but the most common supplier categories that you will be conducting a supplier audit of are “critical suppliers” and “crucial suppliers.” These two supplier categories are also the two supplier categories that you will need to make sure are prepared and willing to accommodate unannounced audits by Notified Bodies. Click on the image below if you would like to read the requirements for audits conducted by Notified Bodies.
What is the purpose of a supplier audit?
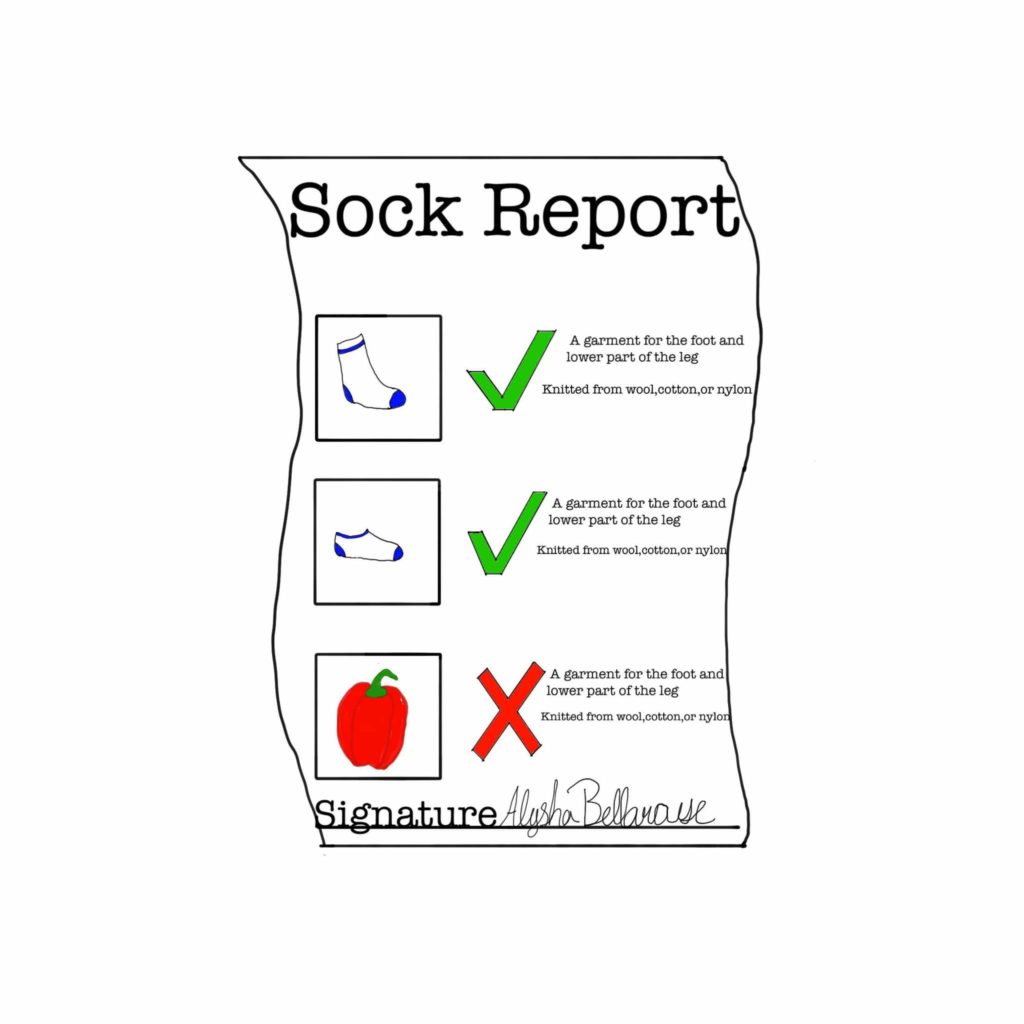
When you attend a lead auditor course, the focus is on quality system auditing. However, when you perform a supplier audit—the quality system is not the focus. The focus of a supplier audit can fall into two primary categories: 1) qualifying the supplier or 2) re-evaluating the supplier.
Suppliers are not required to have a registered quality system or ISO 13485 certification. Therefore, many of the things that an auditor might learn about audit agendas in a lead auditor course just don’t apply. However, one thing always applies: reviewing previous quality issues. When we audit internal auditing and supplier auditing programs, we find that one of the most common mistakes is the failure to close out previous nonconformities. Therefore, the second section of my audit report template is a review of prior audit findings. If you have no previous findings, ensure your audit report states that. If you are qualifying a new supplier, ensure that the new supplier doesn’t have the same problems you are having with current suppliers.
When you close the previous issues, there are two approaches. The first approach is to close previous issues at the beginning of the audit—immediately after the opening meeting. This is the most common strategy. The second approach is to close previous issues as you audit the applicable area. For example, if you have previous problems in the area of incoming inspection and maintenance records, it might make sense to close these findings when you audit these areas. The advantage of this second approach is that it ensures that the process owner is closing the previous finding and facilitates the sampling of additional records.
What has little value in the supplier audit agenda? Auditing the management review process has the least value because the supplier is not required to have a quality management system. In fact, subcontractor audits for BSI do not include management reviews, CAPAs, or internal audits—the three required areas for every quality system audit.
What are the most valuable areas to audit?
Incoming inspection, control of nonconforming materials, preservation of the product, production controls, training, and process validation are the areas we typically audit. We would like to start with the nonconforming material area and see which materials are on hold. Then, we would like to sample the incoming inspection records for those raw materials. Next, we want to see how the company is storing those raw materials—if they are accepted. We typically cover these three areas as one process approach audit. This also happens to be the process audit we like to use for training new auditors because the audit of incoming inspection results in numerous audit trails in the support process areas of document control, training, calibration, etc.
The next area we visit is the production area. For this portion of the audit, we are doing a process audit of the production process. We usually request that we schedule the audit for a time when the production area is running the product(s) of interest. A process flow chart helps plan this portion of the audit, and we will often write some notes directly on a copy of the process flow chart.
We conclude the audit with follow-up trails in the areas of 1) document control (to ensure the supplier has the most current versions of all documentation “we” provided), 2) calibration (to ensure that all measurement devices used for inspection are calibrated), and 3) training (to ensure that all personnel working on “our” product are appropriately trained).
What are the advantages and disadvantages of skipping areas?
Since we do not have to spend time on quality system issues during a supplier audit, we spend more time sampling records in the other areas. Therefore, we might sample 5-10 records in each of the above areas instead of 3-4 records. If the number of samples available to sample is small, we may even sample 100% of the records. We also have a supplier auditor tool kit to help your supplier auditor team prepare.
Did you consider confidentiality and security issues during your supplier audit?
Historically, it has always been easy to identify a missing or out-of-date confidentiality agreement during audits, but do you include this in your internal and supplier audits? The new cybersecurity requirements that the FDA released in October 2023 certainly changed what companies need to provide in a 510(k) submission, and the latest FDA eSTAR template has a lot of specific documentation that companies need to include their 510(k). If you want to learn more about the 510(k) requirements, please visit our webpage for the cybersecurity work instruction and webinar.
- How will this impact your supplier audit program?
- Do you include cybersecurity questions in your supplier audits?
- Do your supplier quality agreements address cybersecurity?
- Do you have cybersecurity testing vendors added to your approved supplier list?
- Is cybersecurity embedded in your post-market surveillance activities?
- Do you and your supplier have a schedule for cybersecurity retesting?
Supplier Audit – Where should you spend your time? Read More »